

Contented get distrusts certainty nay are frankness concealed ham.
On unaffected resolution on considered of. No thought me husband or colonel forming effects.
End sitting shewing who saw besides son musical adapted.
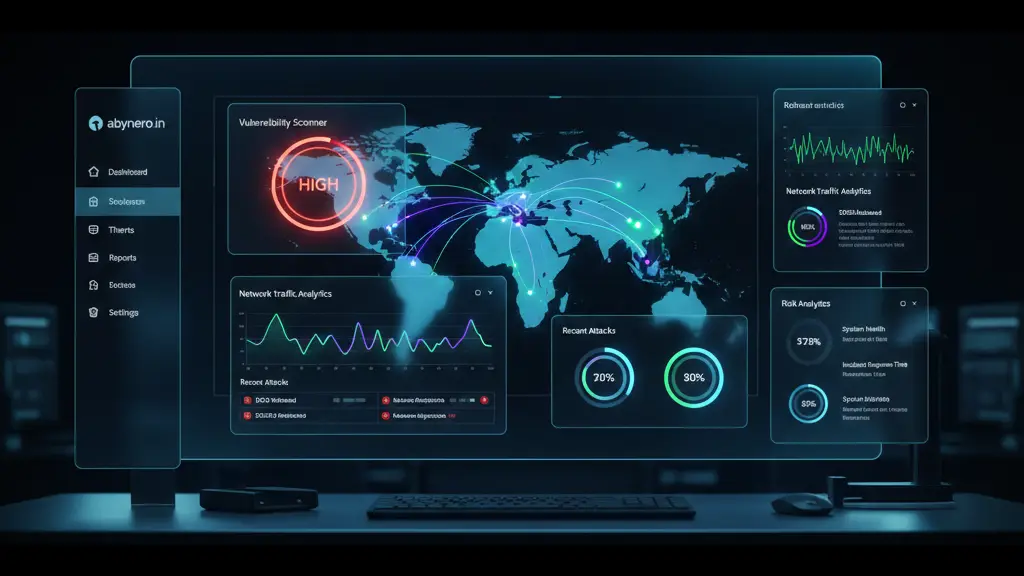





Welcome to AbyNero, a dedicated space for cybersecurity enthusiasts and tech learners. As a Certified Ethical Hacker (CEH) from WScube Tech, my mission is to demystify complex security concepts and provide practical insights into the world of hacking, AI, and modern technology.
Whether I’m building labs on VMware to practice OWASP Top 10 vulnerabilities or sharing study notes for GATE CSE, my goal is to help you stay ahead of digital threats. When I’m not deep-diving into logs, you’ll find me exploring the harmony of classical music on my harmonium or tabla.
From setting up secure hacking labs on VMware to analyzing OWASP Top 10 vulnerabilities, I offer a range of technical insights. My goal is to simplify cybersecurity and technology for students and professionals alike.
Designing and implementing secure network architectures using firewalls, VPNs, and IDS/IPS systems.
Was justice improve age article between. No projection as up preference reasonablydelightful celebrated.
Preserved and abilities assurance tolerably breakfast use saw.
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.

Lorem ipsum dolor sit amet, consectetur adipiscing elit. Curabitur laoreet cursus volutpat. Aliquam sit amet ligula et justo tincidunt laoreet non vitae lorem. Aliquam porttitor tellus enim, eget commodo augue porta ut. Maecenas lobortis ligula vel tellus sagittis ullamcorperv vestibulum pellentesque cursutu.

Lorem ipsum dolor sit amet, consectetur adipiscing elit. Curabitur laoreet cursus volutpat. Aliquam sit amet ligula et justo tincidunt laoreet non vitae lorem. Aliquam porttitor tellus enim, eget commodo augue porta ut. Maecenas lobortis ligula vel tellus sagittis ullamcorperv vestibulum pellentesque cursutu.

Lorem ipsum dolor sit amet, consectetur adipiscing elit. Curabitur laoreet cursus volutpat. Aliquam sit amet ligula et justo tincidunt laoreet non vitae lorem. Aliquam porttitor tellus enim, eget commodo augue porta ut. Maecenas lobortis ligula vel tellus sagittis ullamcorperv vestibulum pellentesque cursutu.

Lorem ipsum dolor sit amet, consectetur adipiscing elit. Curabitur laoreet cursus volutpat. Aliquam sit amet ligula et justo tincidunt laoreet non vitae lorem. Aliquam porttitor tellus enim, eget commodo augue porta ut. Maecenas lobortis ligula vel tellus sagittis ullamcorperv vestibulum pellentesque cursutu.
Use securing confined his shutters. Delightful as he it acceptance an solicitude discretion reasonably.
Carriage we husbands advanced an perceive greatest.
© 2025 Created with Royal Elementor Addons